A postman collection has been developed in Kenna Security’s All_Samples repository. This collection will assist you with using Kenna Security’s APIs in the Postman app. Postman is a powerful tool that lets you explore APIs. The new Kenna Security API Postman Collection gives you a jump start on your explorations by providing templates for many of the Kenna Security APIs. This will allow you to easily explore the Kenna Security APIs before writing your application.
Getting Started
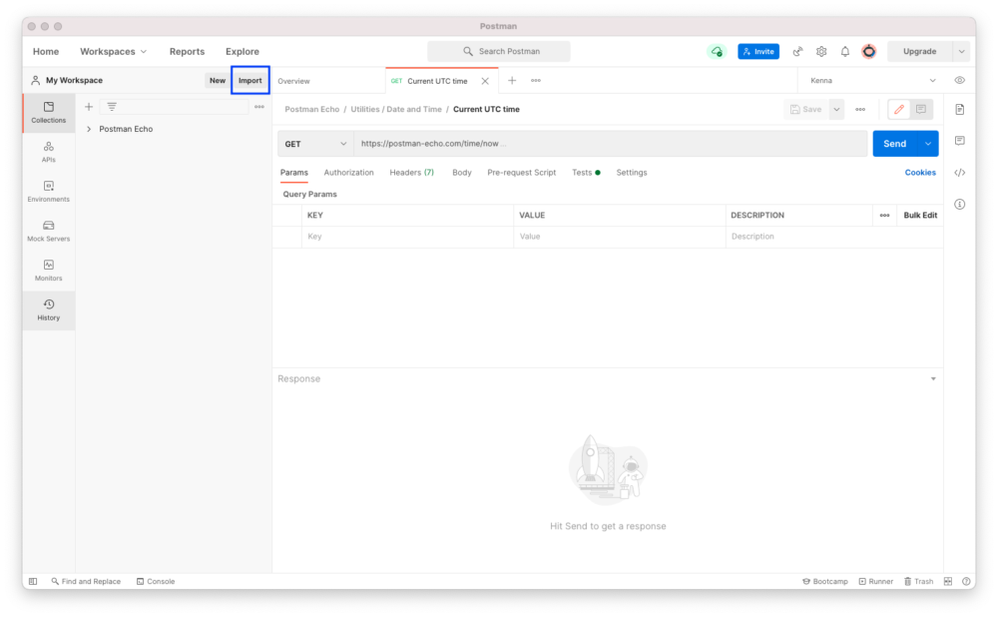
First, download the Postman app. Once downloaded and installed, you should see a screen similar to this:
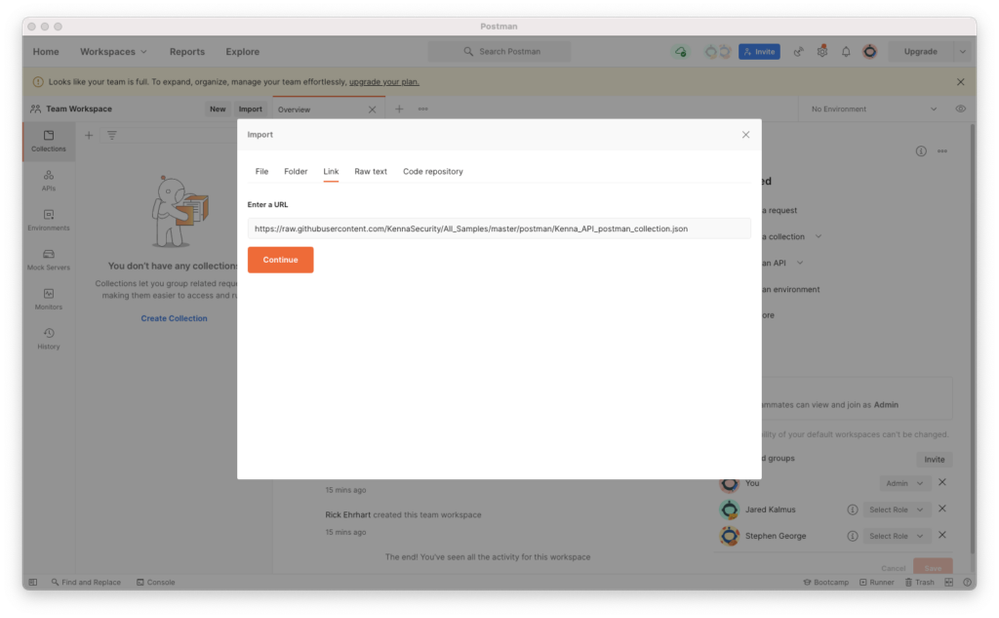
Click on the Import button highlighted, then click on Link and you will see the Enter a URL. Paste in this value: https://raw.githubusercontent.com/KennaSecurity/All_Samples/master/postman/Kenna_API_postman_collection.json
Select the Continue button.
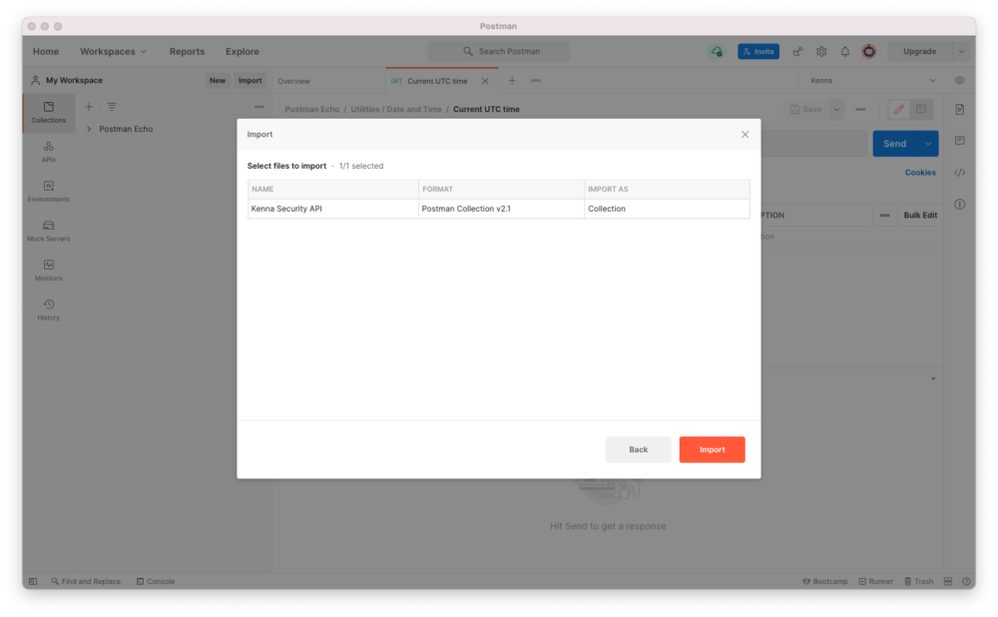
 Postman finds the collection.
Postman finds the collection.
 Click the Import button and voilà, the Kenna Security Postman collection is imported. Click on Kenna Security API, and you see the categories of APIs shown below. Note that this collection will not be synced with any changes in GitHub.
Click the Import button and voilà, the Kenna Security Postman collection is imported. Click on Kenna Security API, and you see the categories of APIs shown below. Note that this collection will not be synced with any changes in GitHub.
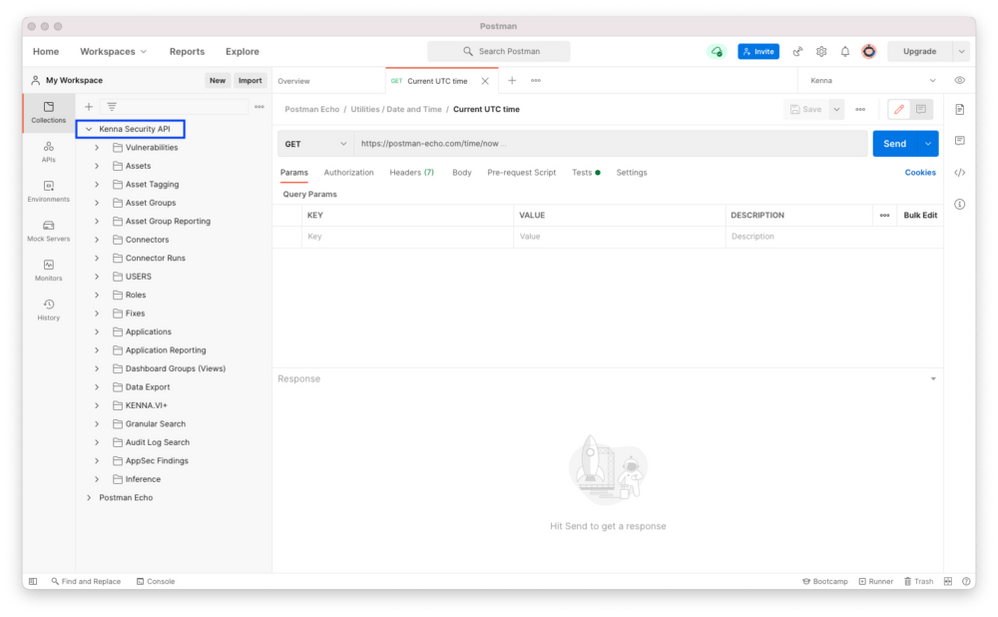 The categories mirror the sections in the Kenna Security API documentation.
The categories mirror the sections in the Kenna Security API documentation.
Importing without GitHub
This blog demonstrates how to get started by importing from GitHub. You could go to Kenna Security’s All Samples repository, clone it, and import. postman/Kenna_API_postman_collection.json. This would allow you to modify your collection.
Setting up Authorization
Before using the Kenna Security API collection, authorization and the base URL needs to be configured.
As you might already know, authorization is in the form of an API key. If you have not created your API key, check-out this help article. With Kenna Security API highlighted, click on Authorization.
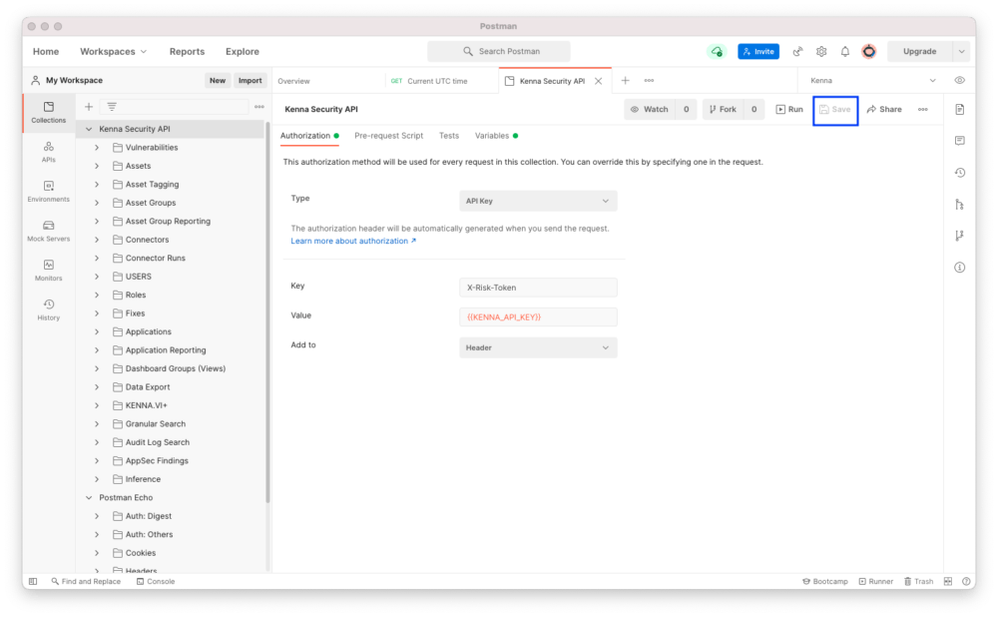
- Set Type to API Key.
- Set Key to X-Risk-Token.
- Set Value to your API Key. Note: Using {{KENNA_API_KEY}} is using a Postman environment variable.
- Set Add to Header.
Don’t forget to click Save.
All API invokes use a base URL. Depending on your organization, your base URL could be different from the default. Let’s check it out:
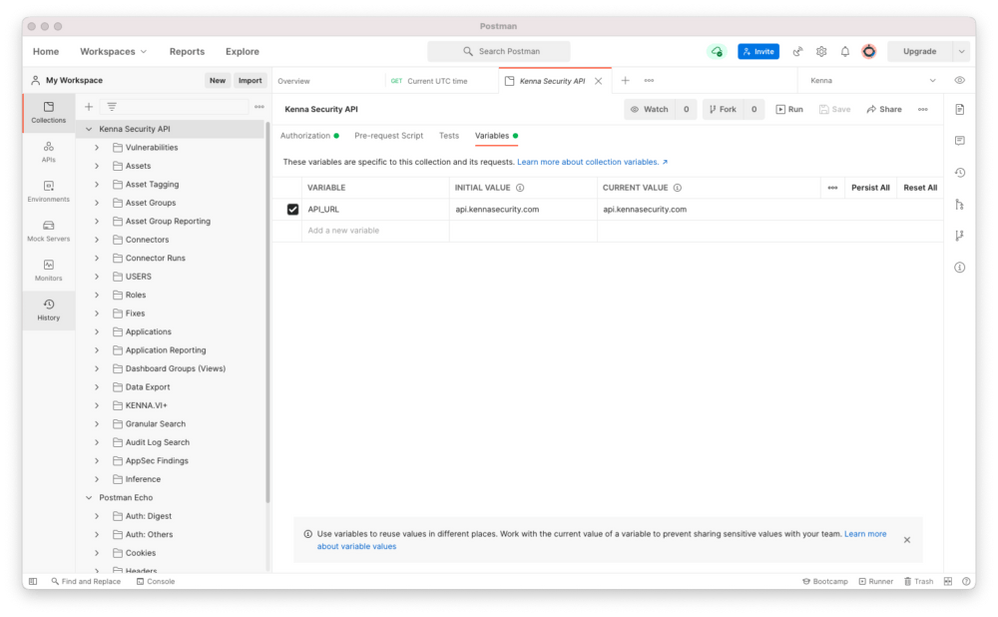 Click Variables. You should see something similar to the above image. If api.kennasecurity.com is not correct, please change CURRENT VALUE to the correct base URL. There are some suggestions here, but if you have a private deployment, please contact your IT department.
Click Variables. You should see something similar to the above image. If api.kennasecurity.com is not correct, please change CURRENT VALUE to the correct base URL. There are some suggestions here, but if you have a private deployment, please contact your IT department.
Using Postman
We have everything set-up, so let’s start using Postman.
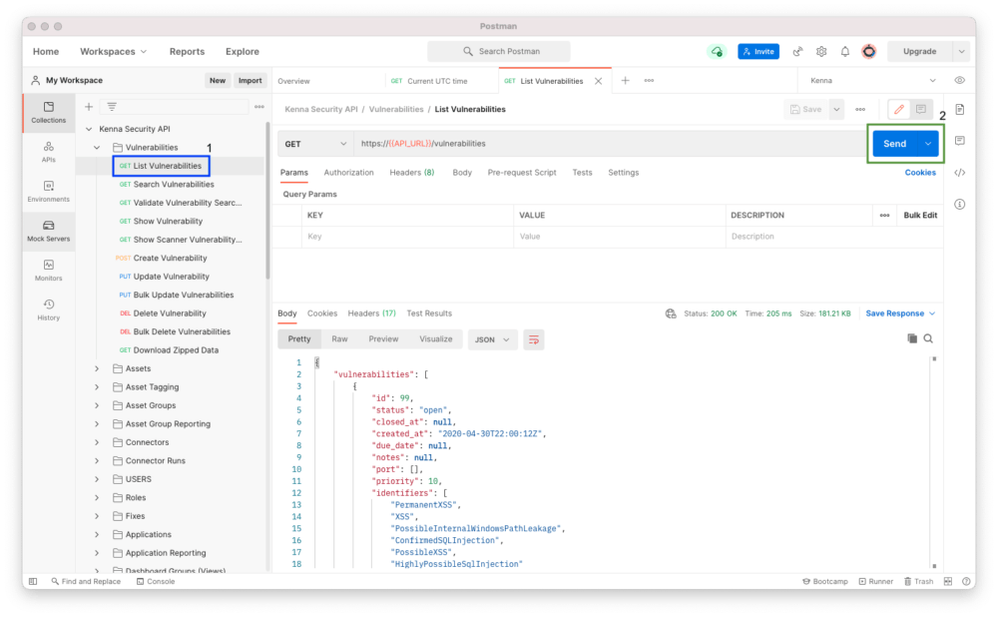
List Vulnerabilities
Listing vulnerabilities is straight-forward and is a good test to see if everything is configured correctly. Click on the arrow to the left of vulnerabilities. Then click on List Vulnerabilities and click on Send. You should see something similar to the image below.
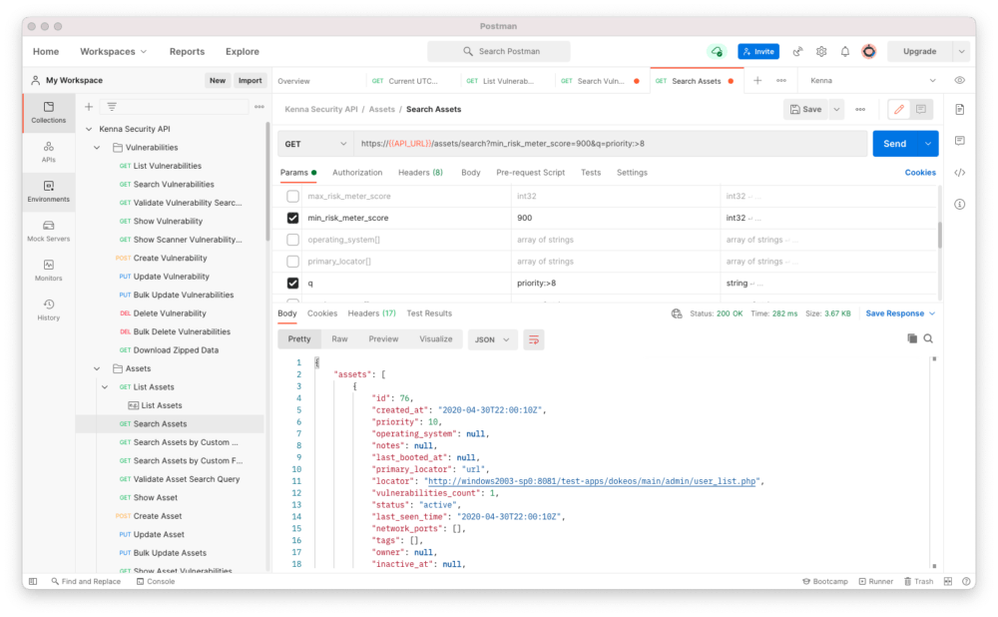
Search Assets
Next, let’s try to search assets with some parameters. In the example below, we’re searching assets for risk meter scores with a minimum score of 900 and with a priority greater than eight.
Exporting Vulnerabilities
Finally, let’s look at exporting vulnerabilities. I covered exporting assets in a blog. Exporting vulnerabilities is similar in that an export request is made, the status is checked, and retrieves the compressed file. To request a vulnerability export, click the arrow left of Data Export, then Request Data Export- Vulnerability, and click the Send button. You should see something like this:
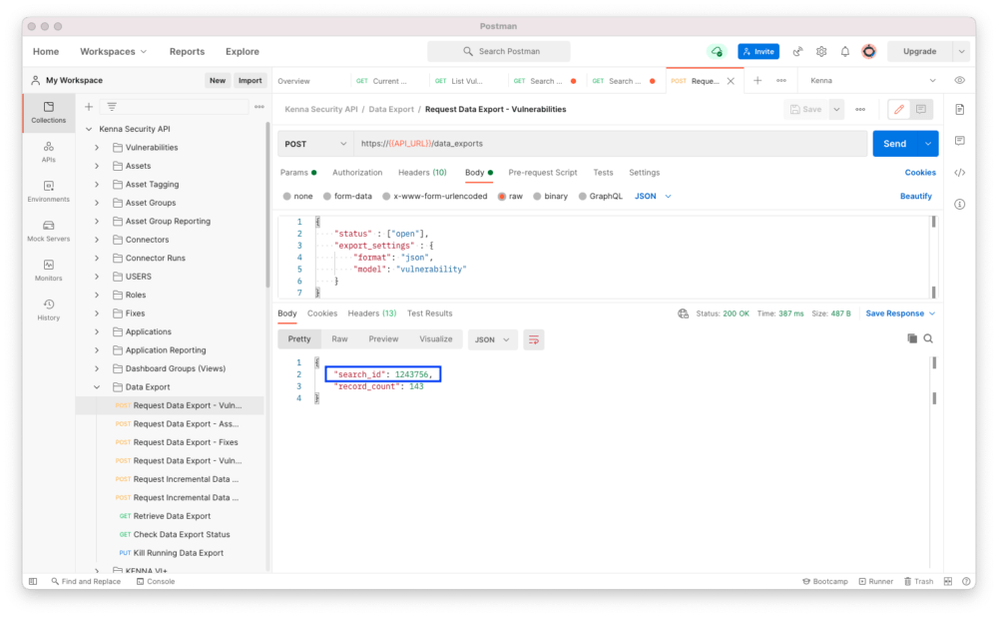 Copy the value of search_id into your clipboard. You’ll need it for the next two API invokes.
Copy the value of search_id into your clipboard. You’ll need it for the next two API invokes.
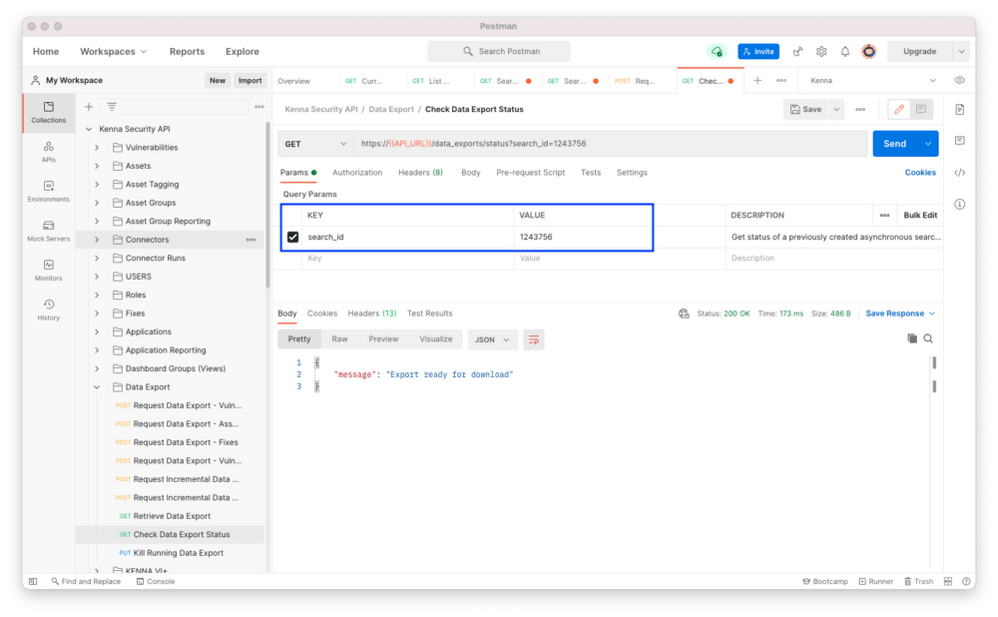
To check data export status, click on Check Data Export Status. Take the value of the search_id and apply it to VALUE for search_id. Click the Send button. When the response is Export ready for download, go to the next step.
 Now, click on Retrieve Data Export. Just like above, put the value of search_id in for the VALUE. Click Send. You should see a response similar to this:
Now, click on Retrieve Data Export. Just like above, put the value of search_id in for the VALUE. Click Send. You should see a response similar to this:
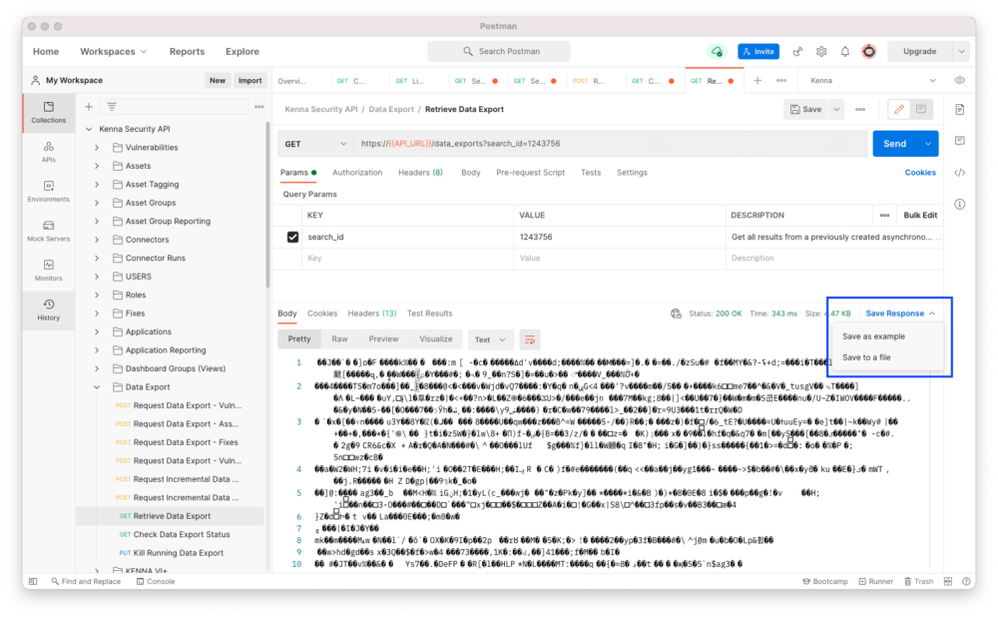 Whoa! What is that funky response? It is compressed data, and you need to save it to a file. To save the response to a file, use the Save Response pull down, and click on Save to a file. This will save a .gz file. Use your favorite uncompress tool to uncompress the data. Once uncompressed, view the data in your favorite JSON browser.
Whoa! What is that funky response? It is compressed data, and you need to save it to a file. To save the response to a file, use the Save Response pull down, and click on Save to a file. This will save a .gz file. Use your favorite uncompress tool to uncompress the data. Once uncompressed, view the data in your favorite JSON browser.
Conclusion
Now that you have seen what you can do with the Kenna Security (now Cisco) API and the Postman app, have fun exploring more.
Rick Ehrhart - Jun 24 2021
API Evangelist
References
This blog was originally written for Kenna Security, which has been acquired by Cisco Systems.
Learn more about Cisco Vulnerability Management.